Surfing the internet is one of the favorite pastimes for a vast majority of people these days. Even though it is harmless most of the time, it needs to be said that it can be quite unsafe if you are not careful about the way you use it. Therefore, it always pays off to have at least some protection against these dangers.
As you can imagine, there is a plethora of software that can help with doing so. However, if we were to choose the most useful ones, we would say VPNs. For those who don’t know what these are, we are talking about software that masks our IP address, and it shows it as some other one, usually from another country.
If you want to check one of these out, be sure to visit VPN download PC. Since there are many VPN software to choose from, finding the best solution for yourself can be a daunting task. That’s why we want to talk about common types of VPN protocols, and therefore, make your choice significantly easier.
Without further ado, let’s begin.
1. WireGuard

The first one we want to address in this list of ours is WireGuard. For those who haven’t heard about it, we are talking about a protocol that was released to the public just a couple of years ago, in 2020. The highlight of this one is that it has quite a fast connection. What makes this possible is only four thousand lines of code, which is pretty small.
Another thing you need to understand about this one is that it is open-source software. It means that it has an active community of developers who are constantly working towards upgrading its existing features and adding several new ones from time to time.
Anyone who has it on their laptop or PC can have a peek into the code, edit it, and share the new code with all the members of the community quite easily. Also, you can be sure that it is quite simple to audit, deploy, and troubleshoot it. Those four thousand lines of code will make that much simpler for you.
2. IKEv2

IKEv2 is another protocol that requires your attention. We are talking about a VPN tunneling protocol that has its secure key session. What needs to be said about this one is that it has encryption which is widely believed to be among the most effective ones. We can compare it to other protocols like L2TP.
The most important thing to know about IKEv2 is that it is quite effective when it comes to reconnecting after short disconnections. Therefore, you will not face any problems in case you need to change the networks, which usually happens when you move from another place to another in search of a new Wi-Fi connection.
3. IPSec

IPsec is a great protocol that’s widely used for correspondence across the network. Accessing certain data means that it will be encrypted the same moment you access it. It has two different modes, the first one being tunneling and the second one being transport mode.
The first one ensures that the whole parcel will be encrypted, and the second one will ensure this data will be protected from potential outside influence. With these two layers of protection, you can be sure that nobody will be able to disrupt the channel. So, you can rest assured it will be protected thought out the journey.
4. PPTP
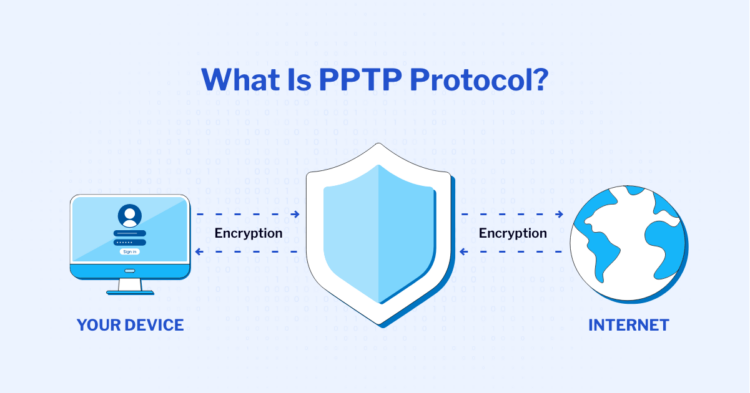
Now we’ve got to the protocol that was established to be a part of pretty much every operating system Microsoft creates. It has been around since the first systems were produced by this company. Naturally, we are talking about a well-known name in this world, the PPTP VPN protocol.
What’s important to understand about this one is that its encryption works between the connection and confining the data packet. What does this mean? Well, it means that this is a fast procedure, but it means it doesn’t provide you with the highest possible security. But that doesn’t have to be bad.
It all depends on what your actual needs are. If you do not need such protection, and you need fast protocol, choosing this one is the way to go. At the same time, we want to say that modern technologies have made it possible for this one to be much more secure than it was in the past.
5. SSTP

The next one we would like to talk about is SSTP. We are talking about one of the oldest ones out there since it has been present in pretty much all the operating systems since mid-2000. Many people are not aware of this fact, but SSTP is widely present in this day and age.
Since this is some kind of exclusive software for Microsoft, its users do not have the opportunity to take a look at the lines of the code, which is a shame. So, those who are interested in learning about the code must find an alternative. Nevertheless, saying that this protocol is not an effective one would be an understatement.
6. OpenVPN

Last but not least, we want to address OpenVPN. As the name of this one says, it is open-source software, which allows third-party developers to use the code and change it to their liking. When it comes to the protocol itself, we are talking about AES-256, which is quite an effective and popular encryption these days.
Since this one is not a built-in element of any sort of device out there, like mobile phones or desktop PCs, it is used solely for third-party users. They use it for overcoming certain firewalls. All in all, it is not the fastest one out there, but it is easily one of the most reliable choices you can make out there.
The Bottom Line
Understanding VPN protocols is an absolute must when you are about to make a choice. Here, we’ve discussed some of the most important ones. We’ve named all their characteristics which will make sure your choice is much simpler and smoother.
 Hi Boox Popular Magazine 2025
Hi Boox Popular Magazine 2025



